Trust Nothing: Using the Misinformation Era Against Attackers
Trust Nothing: Using the Misinformation Era Against Attackers
In April 1943, a Spanish fisherman pulled a bloated corpse from the waters off Huelva. Chained to its wrist: a briefcase of military documents that would alter World War II. The body was dressed as Major William Martin, Royal Marines. An identity that didn’t exist. British intelligence had taken a Welsh vagrant’s corpse, fabricated love letters, an overdue tailor’s bill, and fake invasion plans pointing to Greece and Sardinia. The Germans stole the intelligence rather than being handed it, so they believed it completely. Hitler repositioned divisions. Weeks later, Allied forces landed on the real target, Sicily, facing a fraction of the expected resistance. The most consequential intelligence operation of the war required no firepower, no technology, no army. Just a dead man, a briefcase, and documents designed to be found.
Eighty years later, the same principle remains devastatingly underused in cybersecurity. Organizations spend millions keeping attackers out — but perimeter defenses fail, credentials get stolen, and once someone is inside moving laterally, most security stacks fall silent. What’s missing isn’t another wall. It’s a smart trap.
Today, unfortunately, we live in an era defined by misinformation. Deepfakes, fabricated news, AI-generated content. Society is learning the hard way that not everything presented as truth can be trusted. This erosion of certainty is typically framed as a problem. And it is! But for defenders, it’s an opportunity. If attackers can no longer assume that what they find is real, the network itself becomes hostile territory. The concept of deception – planting something fake that serves no purpose other than to be touched by someone who shouldn’t be there – gives defenders an asymmetric advantage. A single interaction with a decoy file, a fake credential, or a tripwire DNS entry is a high-fidelity signal with almost zero false positives. Legitimate users have no reason to open backup_domain_admin_creds.xlsx. But attackers can’t resist it!
Here’s where it gets interesting: even if adversaries know you deploy deception, it doesn’t neutralize the technique. It amplifies the psychological burden. Every file becomes suspect. Every credential could be poisoned. They can’t distinguish between an honest mistake, where an overworked admin left creds.txt on a shared drive, and a deliberate trap waiting to expose them. Do they use the credentials and risk triggering an alert? Do they ignore them and potentially miss legitimate access? Hesitation costs time. Interaction costs their anonymity. Either outcome benefits the defender. Just like German intelligence in 1943, modern adversaries will pursue what looks valuable. But now they must do so knowing the ground beneath them might not be real. That uncertainty is a weapon you’re not using.
And some might assume this sounds quite complex to implement. They would be wrong. There are even free services from trusted reputable companies supporting this, in which you don’t even need to sign up. Just submit the email that gets notified. And you don’t need many alternatives spread around your infrastructure. Maybe just one trap inside your network in an enticing place would do the trick.
Let’s just try a Word document.
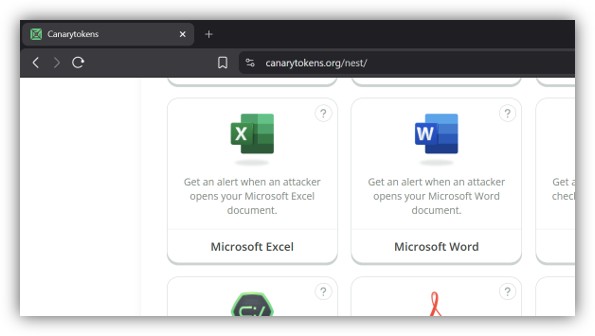
On this page alone, one has multiple alternatives, including Credit Card numbers that if used will obviously not work, but will trigger a notification to the submitted email. But for this example, I chose Microsoft Word trap, as I mentioned before.

And then the file is provided to me.

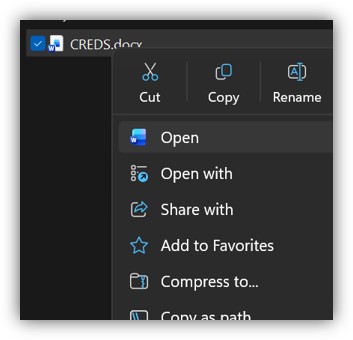
Notice the warning letting me know I can rename it, to something more appealing to attackers.
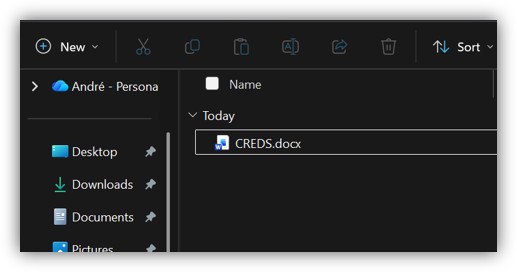
From an ethical hacker’s perspective, I have to admit: this is so very tempting.
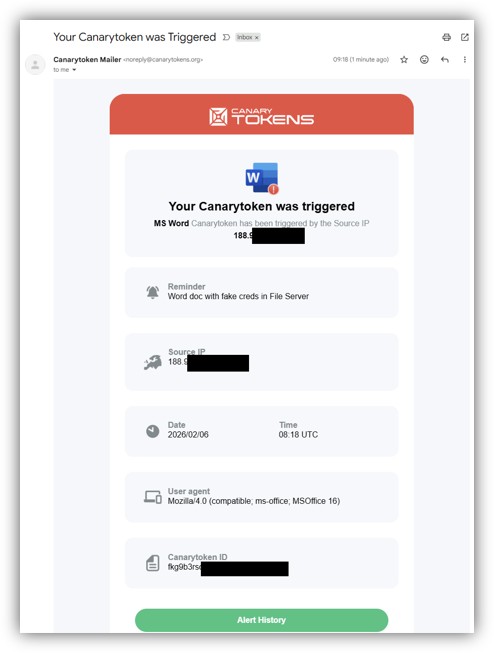
And opening this file inevitably triggers the notification in the submitted mailbox.
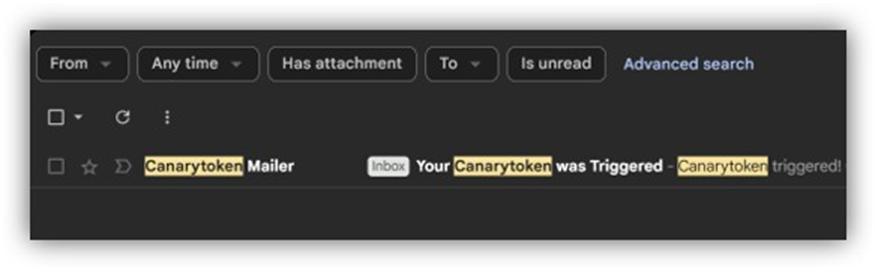
And now you know with an incredibly high level of confidence that someone inside your network is doing something they should not be doing.
In the end, deception is not about tricks or theatrics. It’s about shifting the balance of certainty. When attackers can no longer trust what they see inside your environment, exploration becomes risk, and curiosity becomes liability. In an age where misinformation defines the battlefield, defenders may finally have permission to use uncertainty as a deliberate, strategic advantage.


